DevSecOps aims to maintain the same standard of operations and development from the start of the process through the maintenance phase. Assuring a smooth transition from traditional procedures to advanced DevOps systems is necessary to mitigate this, and organizations should use a variety of best practices ISmile experts prefer to implement DevSecOps:
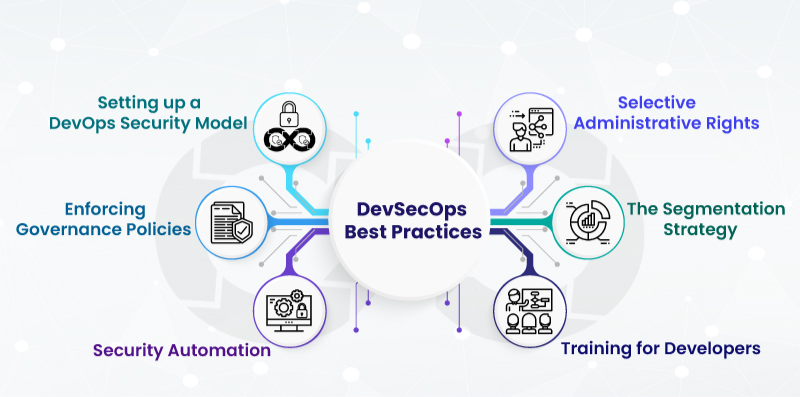
Setting up a DevOps security model
Incorporating Identity and Access Management (IAM), cybersecurity precautions, code review, configuration, and governance through DevOps activities is perhaps the first step in adopting the DevSecOps approach.
It is simple to assure the secure delivery of products and reduce the likelihood of glitches and bug-fixing. It recalls following product releases by assigning security to the various stages of the DevOps workflow.
Enforcing governance policies
Establishing governance guidelines and IT standards that guarantee data protection is one of the core components of the DevSecOps concept. The duties and responsibilities of the board, committee and officials would be impacted in some way because organizational activities are constantly changing.
Therefore, it is crucial to adhere to policies and processes for data protection to maintain organizational openness. Creating transparency will also aid in preventing and repairing any damage caused by questionable internal threat activity.
Security automation
Security teams must be quick and flexible during the DevOps cycle development stage to provide high security, necessitating automation for minimizing errors and maximizing efficiency. Organizations can reduce expenses, work hours, and resource usage through vulnerability testing and privilege control.
Training for developers
Obtaining complete participation from your stakeholders is one of the major hurdles in adopting DevSecOps. Different teams, such as development, operations, and security, work in isolation, spread their agendas and prioritize their jobs. Getting the development team to devote the proper resources and time to learning secure code can be difficult.
The segmentation strategy
The segmentation approach is another way to apply DevSecOps by getting rid of hackers and attackers. This is an excellent example of the divide and conquers method in action. Limiting access to the application resource server removes the problems a continuous process brings.
Thus, segmenting the network makes it very difficult for hackers or other attackers to access the data in one go without authorization. This is an effective method for reducing the hazards posed by hackers and keeping errors to a minimum.
Administrative discretion
Keeping privileges at a minimum is one of the best strategies to reduce internal risks and errors. This contributes to limiting the quantity of data that anyone can access. It is also a fantastic approach to assist local computers in storing crucial information for controlling access.
How ISmile Can Help
ISmile Technologies is a North American IT service provider that delivers DevSecOps through an approach that makes security an integral part of DevOps procedures. We favour creating bug-free systems and have all the gaps closed at the outset of the development process.